In this Article
For a customer in the medical technology sector, we implemented a connection between SAP and Cryptshare. This solution provided both the security that our customer was looking for and added benefits. The below is an overview of the solution, and how SEAL Systems was able to help.
Initial Situation
For years, SEAL Systems provided an initial solution for this requirement by sending orders via email. (Read more about this solution on our page purchase processes.) However, the customer no longer wanted to transmit the additional documents by unsecured email. Instead, they wanted to exchange the documents via a secure communication.
So, since the company already used Cryptshare as a collaboration platform for secure file transfer for other processes, the new requirement for SEAL Systems was to create a connection between our processes and Cryptshare.
How Was the Solution Implemented?
In SAP, the standard procedures from SEAL Systems are used for document determination. The result of this document determination is an output request, in which the order and the additional documents are combined
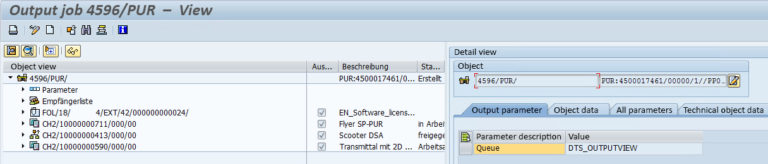
Screenshot: Output order with additional documents in Document Distribution Director.
For implementing the Cryptshare interface, the SEAL Systems standard process was extended as follows:
- Cryptshare storage yes/no
A new parameter was added to decide where the job is stored. If the parameter is set, the request is stored on Cryptshare. Otherwise, it is delivered by email. - Creation of a unique password for Cryptshare
A secure password is created for each job that is stored on Cryptshare. - Sending an email with the order and the Cryptshare password
All documents that should not be made available to the supplier via Cryptshare are sent to the supplier as email attachments. Additionally, the password for accessing Cryptshare is attached to this email. - Storage of the documents on Cryptshare
All documents marked for storage on Cryptshare are loaded on the Cryptshare server. The created password ( #2) is defined for access. - Cryptshare mail to the supplier
As soon as the upload is finished, Cryptshare sends a second email to the supplier with a link to the files in the Cryptshare. The supplier can access and download these files with the received password.
The Advantages of a Cryptshare Connection from SEAL Systems:
- Protection of confidential information
- Usable for everyone
- Legal requirements are complied with
- Send files of any size securely
- High user acceptance through simple operation
The SAP Cryptshare connection is of course not limited to the ordering process described here, but can also be used with any other SAP processes, such as maintenance, service or similar.
Contact us
Fill out the form below to receive more information or let us know what we can do for you.
Additional Topics for this Article
Supplement your SAP purchasing documents with all accompanying documents